Name the new value as AllowInsecureGuestAuth and set its value data to 1. You should be able to access CIFS / SMB / Samba network shares instantly without login. Update: If you’re using a Microsoft Account (MSA) to sign into Windows 10, you may also need to create a domain user account with proper access permissions configured in Samba or Windows Shared Folders on the remote server for. May 08, 2012 However, MS is making it more and more difficult to share using SMB in Windows. You have to turn off Homegroup and do all sorts of other messy things. The following is a guide to quickly and easily turn SMB sharing on in Windows 7. Preparation As a. The Ransomware targets the vulnerabilities of the SMB service of the Windows operating system to propagate. SMB or Server Message Block is a network file sharing protocol meant for sharing files. Jun 19, 2013 Steps to Enable and Disable SMB protocols on the SMB client. The below steps applies to Windows Vista, Windows Server 2008, Windows 7, Windows Server 2008 R2, Windows 8, and Windows Server 2012. Disables the SMBv1 on the SMB client by running the below commands: sc.exe config lanmanworkstation depend= bowser /mrxsmb20/ nsi. However, MS is making it more and more difficult to share using SMB in Windows. You have to turn off Homegroup and do all sorts of other messy things. The following is a guide to quickly and easily turn SMB sharing on in Windows 7. Preparation As a initial step, you should be connected to your network. This video will guide you on creating a shared folder on your Windows 7 and 10. Its Part 1 of 2 videos to set up SMB scanning on your Konica, Kyocera, Canon.
The following is a brief summary recent SMB v1 vulnerabilities, ransomware and an enterprise approach to disabling SMB v1 via Group Policy.
Why SMB v1 Isn’t Safe (September 16, 2016)
Ned Pyle wrote a blog post in September of 2016 on why SMBv1 isn’t safe where he stated that if your clients use SMB1, then a man-in-the-middle can tell your client to ignore security settings like:
- Pre-authentication Integrity (SMB 3.1.1+). Protects against security downgrade attacks.
- Secure Dialect Negotiation (SMB 3.0, 3.02). Protects against security downgrade attacks.
- Encryption (SMB 3.0+). Prevents inspection of data on the wire, MiTM attacks. In SMB 3.1.1 encryption performance is even better than signing!
- Insecure guest auth blocking (SMB 3.0+ on Windows 10+) . Protects against MiTM attacks.
- Better message signing (SMB 2.02+). HMAC SHA-256 replaces MD5 as the hashing algorithm in SMB 2.02, SMB 2.1 and AES-CMAC replaces that in SMB 3.0+. Signing performance increases in SMB2 and 3.
“...If your clients use SMB1, then a man-in-the-middle can tell your client to ignore all the above” Please review Ned Pyle’s full blog article on Why SMB1 isn’t safe
TechNet Guidance on Enabling/Disabling SMBv1/2/3 (February 28, 2017)
Microsoft in February updated and published a TechNet article on how to enable or disable various versions of SMB using:
- The Registry Editor for LanmanServer
- PowerShell’s Set-SmbServerConfiguration for SMB server
- sc.exe with config options for lanmanworkstation
Caution! While these tools can work for quick configuration changes, this combination approach is not very manageable in large-scale managed enterprise environments where consistent configuration is required.
Microsoft Published Security Bulletin MS17-010 (March 14, 2017)
Microsoft released a critical Security Update for Microsoft Windows SMB Server security bulletin and updates under KB 4013389 along with a host of security updates for all supported versions of Windows under MS17-010.
Enter Global Ransomware Attack (May 12, 2017)
The WannaCrypt ransomware attack began exploiting the SMB v1 server vulnerability and began spreading globally on May 12.
U.S. CERT Advisory (May 12, 2017)
CERT issued an advisor for Indicators Associated With WannaCry Ransomware with the following recommendations:
Apply the patch (MS17-010). If the patch cannot be applied, consider:
- Disabling SMBv1 and
- blocking all versions of SMB at the network boundary by blocking TCP port 445 with related protocols on UDP ports 137-138 and TCP port 139, for all boundary devices.
SMB Vulnerability Patch for Windows XP & Server 2003 (May 13, 2017)
Microsoft then released SMB security patches for Windows XP and Server 2003 on May 13, 2017.
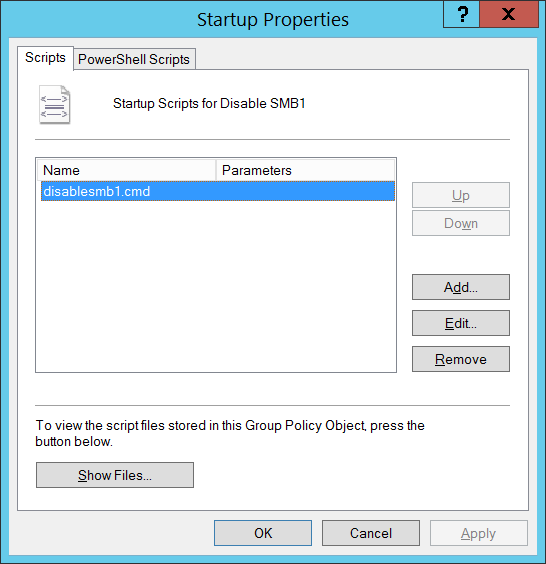
Enterprise Approach to Disable SMB v1 using GPO
Certainly, it’s important to patch against the known SMB v1 vulnerabilities released in MS17-010 and subsequent KB 4013389 for Windows XP/2003. However because of numerous variants of WannaCrypt and these other known security issues with SMB v1 (e.g. man-in the middle); many organizations have issued mandates to completely disable SMBv1 as strategic security countermeasure against future threats.
An enterprise approach to disabling SMB v1 is to use Active Directory (AD) Group Policy preferences to configure and enforce the registry settings related to disabling SMBv1 client and server components for Windows Vista and Server 2008 and later.
Group Policy registry preference items allow you to create, update, replace, and delete keys and values in the Windows registry. The following are the registry keys that need to be created or updated to disable SMB v1.
Disable SMBv1 Server with Group Policy:
This will configure the following new item in the registry
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesLanmanServerParameters
Registry entry: SMB1 REG_DWORD: 0 = Disabled
To configure this using Group Policy:
- Open the Group Policy Management Console. Right-click the Group Policy object (GPO) that should contain the new preference item, and then click Edit.
- In the console tree under Computer Configuration, expand the Preferences folder, and then expand the Windows Settings folder.
- Right-click the Registry node, point to New, and select Registry Item.
In the New Registry Properties dialog box, select the following:
- Action: Create
- Hive: HKEY_LOCAL_MACHINE
- Key Path: SYSTEMCurrentControlSetServicesLanmanServerParameters
- Value name: SMB1
- Value type: REG_DWORD
- Value data: 0
This disables the SMBv1 Server components. This Group Policy needs to be applied to all necessary workstations, servers, and domain controllers in the domain.
Note:WMI filters can also be set to exclude unsupported operating systems or selected exclusions such as Windows XP.
Caution! Be careful when making these changes on domain controllers where legacy Windows XP or older Linux and 3rd party systems (that do not support SMBv2 or SMBv3) require access to SYSVOL or other file shares where SMB v1 is being disabled.
Disable SMBv1 Client with Group Policy:
To disable the SMBv1 client the services registry key needs to be updated to disable the start of MRxSMB10 and then the dependency on MRxSMB10 needs to be removed from the entry for LanmanWorkstation so that it can start normally without requiring MRxSMB10 to first start.
This will update and replace the default values in the following 2 items in the registry
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetservicesmrxsmb10
Registry entry: Start REG_DWORD: 4 = Disabled
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesLanmanWorkstation
Registry entry: DependOnService REG_MULTI_SZ: “Bowser','MRxSmb20','NSI'
Note: The default included MRxSMB10 which is now removed as dependency
To configure this using Group Policy:
- Open the Group Policy Management Console. Right-click the Group Policy object (GPO) that should contain the new preference item, and then click Edit.
- In the console tree under Computer Configuration, expand the Preferences folder, and then expand the Windows Settings folder.
- Right-click the Registry node, point to New, and select Registry Item.
In the New Registry Properties dialog box, select the following:
- Action: Update
- Hive: HKEY_LOCAL_MACHINE
- Key Path: SYSTEMCurrentControlSetservicesmrxsmb10
- Value name: Start
- Value type: REG_DWORD
- Value data: 4
Then remove the dependency on the MRxSMB10 that was just disabled
In the New Registry Properties dialog box, select the following:
- Action: Replace
- Hive: HKEY_LOCAL_MACHINE
- Key Path: SYSTEMCurrentControlSetServicesLanmanWorkstation
- Value name: DependOnService
- Value type REG_MULTI_SZ
- Value data:
- Bowser
- MRxSmb20
- NSI
Note: These 3 strings will not have bullets (see below)
The default value includes MRxSMB10 in many versions of Windows, so by replacing them with this multi-value string, it is in effect removing MRxSMB10 as a dependency for LanmanServer and going from four default values down to just these three values above.
Note: When using Group Policy Management Console, there is no need to use quotation marks or commas. Just type the each entry on individual lines as shown above:
Windows 7 Enable Smb Sharing
Reboot Required
After the policy has applied and the registry settings are in place, the targeted systems must be rebooted before SMB v1 is disabled.
Windows 7 Smb Settings
Summary
If all the settings are in the same Group Policy Object (GPO), Group Policy Management will show the settings below.
Testing and Validation
Once these are configured, then allow the policy to replicate and update. As necessary for testing, run gpupdate /force from a CMD.EXE prompt and then review the target machines to ensure the registry settings are getting applied correctly. Make sure SMB v2 and SMB v3 is functioning for all other systems in the environment.
Caution! Don't forget to reboot the targeted systems.